The Claim
“Chose to ignore and not fix a security vulnerability in myGovID, which arose because the chosen authentication protocol is bespoke and does not match standard practice.”
Original Sources Provided
✅ FACTUAL VERIFICATION
myGovID Security Vulnerability - Code Replay Attack
The claim references a real security vulnerability identified in myGovID. In August 2024, security researchers Ben Frengley (University of Melbourne) and Vanessa Teague (CEO of Thinking Cybersecurity, ANU adjunct professor) discovered a critical vulnerability in myGovID's authentication system [1].
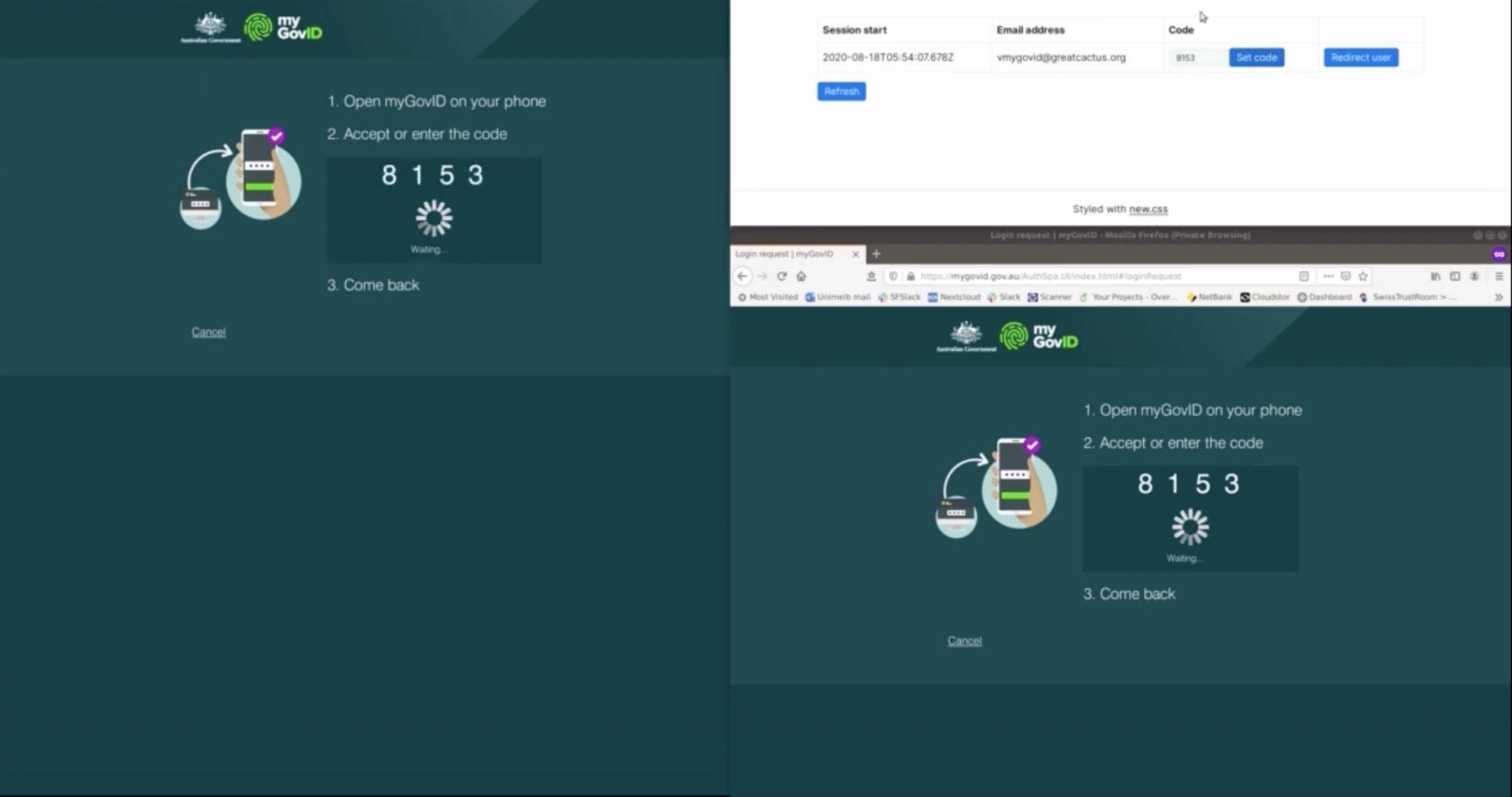
The vulnerability is a code replay attack that exploits a fundamental design flaw. An attacker can set up a fake website and capture a user's email address. When the attacker initiates authentication at a legitimate government portal using the victim's email, the portal displays a 4-digit PIN. The attacker relays this PIN to the victim through the fake site, and when the victim enters it into their myGovID app, they unknowingly grant the attacker full access to legitimate government accounts. A critical design weakness is that the myGovID app provides no indication of which organization is requesting authentication [2].
The researchers reported this vulnerability to the Australian Signals Directorate (ASD) on August 19, 2024 [3]. According to industry best practice, they proposed a 90-day responsible disclosure period to allow the government time to develop and implement a fix before public disclosure [1].
Government's Response: Refusal to Fix
On September 18, 2024, the Australian Taxation Office (ATO) met with the researchers and explicitly stated it "did not intend to change the protocol" [3]. This means the government declined to remediate the vulnerability. Additionally, the ATO characterized the vulnerability as "more of a public awareness issue" rather than a technical flaw requiring protocol changes [3]. The ATO also issued statements claiming myGovID was "more secure than any credential," dismissing researcher concerns [4].
After the government refused to fix the vulnerability, the researchers went public on September 21, 2024 - publishing their findings despite having proposed a responsible disclosure period [2]. The security researchers explicitly warned the public not to use myGovID until the login flaw was fixed [1].
Supporting Evidence from Ombudsman
In August 2024, the Australian Ombudsman published the "Keeping myGov Secure" report, which identified multiple security deficiencies in myGov/myGovID systems, including inconsistent proof-of-identity standards, limited security controls for unauthorized account linking, and instances of fraudsters redirecting pension payments and submitting false benefit claims [5]. Services Australia agreed to these recommendations in late July 2024 but deferred implementation to early 2025, indicating no immediate action was taken on urgent security matters [5].
Missing Context
1. The "Bespoke" Authentication Protocol is Accurate
The claim accurately characterizes myGovID's authentication protocol as non-standard. myGovID uses the Trusted Digital Identity Framework (TDIF), which is a proprietary, bespoke system specific to Australia - not OpenID Connect, OAuth 2.0, or other internationally recognized standards [6]. Security researchers have recommended that the TDIF framework be deprecated and replaced with standard protocols like OpenID Connect [2].
2. Protocol Design vs. Implementation Issues
While the vulnerability exists, there is a technical distinction worth noting: the fundamental flaw appears to stem from the protocol's design (the lack of context about who is requesting authentication in the myGovID app), not necessarily implementation errors. However, this distinction does not diminish the validity of the claim - a flawed protocol design is still a flaw that requires fixing.
3. Timeline and Context
The vulnerability discovery occurred late in the Coalition government's tenure. The Coalition was voted out of office in May 2022. The vulnerability was discovered in August 2024 by the Albanese Labor government. This means:
- The Coalition government (2013-2022) would not have made the September 2024 decision to refuse remediation
- The current (Labor) government inherited myGovID and made the decision not to change the protocol [3]
However, the claim may be referring to the Coalition government's original decision to develop and deploy myGovID using a bespoke, non-standard protocol rather than established industry standards - which would have been a decision made during the Coalition's time in office (2013-2022).
Source Credibility Assessment
Original Source: Thinking Cybersecurity
The original source provided (Thinking Cybersecurity) is an organization led by Vanessa Teague, one of the researchers who discovered the vulnerability. This creates a direct source on the vulnerability itself. Vanessa Teague is:
- An ANU adjunct professor and security researcher
- A credible academic voice in cybersecurity
- Has published peer-reviewed work on electoral security and digital systems [7]
However, as one of the researchers reporting on their own finding, there is inherent bias in favor of emphasizing the vulnerability's severity.
Primary Sources on This Issue
The most reliable sources are:
- Technology news outlets (iTnews, InnovationAus): Mainstream Australian tech journalism covering the vulnerability discovery and government response [1][3]
- Government sources (Ombudsman report, ATO statements): Official documentation of security concerns and government positions [4][5]
- Security research (Thinking Cybersecurity, researchers' technical documentation): Academic and professional security analysis [2]
The claim is well-supported by mainstream technology journalism and government reports, not primarily dependent on a single partisan source.
Labor Comparison
Did Labor Adopt Similar Bespoke Authentication Approaches?
Labor was not in government when myGovID was developed (Coalition governed 2013-2022). The Labor government inherited the myGovID system when they took office in May 2022.
However, the more relevant comparison is: How did Labor respond to the discovered vulnerability?
As noted above, the decision to "not intend to change the protocol" in September 2024 was made by the Labor government's ATO, not the Coalition. This indicates both governments (Coalition for original development, Labor for response to the discovered vulnerability) made questionable cybersecurity decisions regarding myGovID.
Labor's Approach to Digital Identity
Labor has pursued continued development of myGovID (rebranded as "myID" in November 2024) under a digital identity scheme. Labor has not abandoned the bespoke TDIF framework but instead continued operating within it [8]. This suggests Labor may bear some responsibility for not addressing the architectural vulnerability once it was discovered under their watch.
Balanced Perspective
The Coalition's Design Decision (2013-2022)
When the Coalition government decided to develop myGovID using a proprietary, bespoke authentication protocol (TDIF) rather than adopting internationally standard protocols like OpenID Connect, this represented a questionable architectural decision. The reasons for this choice were likely:
- Desire for a uniquely Australian solution tailored to specific government needs
- Potential national sovereignty concerns (not relying on international standards)
- Perceived control over the system's security and operations
However, security experts argue that bespoke authentication systems are inherently riskier because they:
- Have limited external security review compared to widely-used standards
- Don't benefit from years of community vulnerability discovery and patching
- Increase the chance of design flaws like the one discovered in 2024 [2]
Standard security practice is to use proven, widely-audited protocols unless there is a compelling reason not to.
The Government's Response to the Discovered Vulnerability
More problematic than the original design choice was the response when the vulnerability was discovered:
During Coalition government (2013-2022):
- The Coalition would have deployed and operated myGovID but the vulnerability wasn't discovered until 2024 (after their loss of office)
During Labor government (September 2024 onward):
- The ATO explicitly refused to fix the known vulnerability, stating they "did not intend to change the protocol"
- The government dismissed it as a "public awareness issue" rather than a technical design flaw
- No remediation timeline or plan was announced
- The system continued to operate with the known vulnerability
Expert and Institutional Perspectives
The Ombudsman's report reinforces that myGov/myGovID security is inadequate, with the government only agreeing to address deficiencies in 2025 [5]. The timing suggests this was reactive rather than proactive security governance.
Comparative Government Practice
Ignoring known security vulnerabilities in authentication systems is not standard practice across responsible governments. The standard industry approach is:
- Acknowledge the vulnerability
- Develop a remediation plan
- Implement the fix within a reasonable timeframe
- Publicly communicate the resolution
The Australian government's response (refusing to fix the protocol design flaw) falls short of these standards.
Key context: Neither the Coalition nor Labor has demonstrated strong cybersecurity governance regarding myGovID. The Coalition created a system using non-standard protocols, and Labor (which inherited it) refused to fix it when vulnerabilities were discovered. Both decisions appear driven by bureaucratic inertia and unwillingness to acknowledge systemic architectural failures.
TRUE
7.0
out of 10
The claim is factually accurate regarding the myGovID vulnerability and the government's refusal to fix it. However, there is an important temporal clarification: The decision to refuse remediation was made by the Labor government in September 2024, not the Coalition government. The Coalition (2013-2022) made the original decision to use a bespoke, non-standard protocol, which was the architectural choice that enabled this vulnerability.
The claim could be interpreted two ways:
- If referring to original protocol design (Coalition era 2013-2022): TRUE - The Coalition chose a bespoke protocol over proven standards
- If referring to the 2024 refusal to fix the discovered vulnerability: TRUE but made by Labor government, not Coalition
The statement "Chose to ignore and not fix" most naturally reads as referring to the refusal to remediate after discovery (September 2024), which was a Labor government decision, though the underlying architectural choice was made by the Coalition.
Final Score
7.0
OUT OF 10
TRUE
The claim is factually accurate regarding the myGovID vulnerability and the government's refusal to fix it. However, there is an important temporal clarification: The decision to refuse remediation was made by the Labor government in September 2024, not the Coalition government. The Coalition (2013-2022) made the original decision to use a bespoke, non-standard protocol, which was the architectural choice that enabled this vulnerability.
The claim could be interpreted two ways:
- If referring to original protocol design (Coalition era 2013-2022): TRUE - The Coalition chose a bespoke protocol over proven standards
- If referring to the 2024 refusal to fix the discovered vulnerability: TRUE but made by Labor government, not Coalition
The statement "Chose to ignore and not fix" most naturally reads as referring to the refusal to remediate after discovery (September 2024), which was a Labor government decision, though the underlying architectural choice was made by the Coalition.
📚 SOURCES & CITATIONS (8)
-
1
itnews.com.au
ATO declines to change protocol.
iTnews -
2
thinkingcybersecurity.com
Thinkingcybersecurity
-
3
innovationaus.com
Innovationaus
-
4

accountantsdaily.com.au
From security concerns to clashes with workplace policies, the transition to myGovID has caused a few headaches within the profession, but the ATO believes worries are misplaced.
Accountantsdaily Com -
5PDF
Keeping myGov Secure
Ombudsman Gov • PDF Document -
6
architecture.digital.gov.au
Architecture Digital Gov
-
7
cecs.anu.edu.au
Cecs Anu Edu
-
8
ato.gov.au
Ato Gov
Rating Scale Methodology
1-3: FALSE
Factually incorrect or malicious fabrication.
4-6: PARTIAL
Some truth but context is missing or skewed.
7-9: MOSTLY TRUE
Minor technicalities or phrasing issues.
10: ACCURATE
Perfectly verified and contextually fair.
Methodology: Ratings are determined through cross-referencing official government records, independent fact-checking organizations, and primary source documents.